@Zackster beat me to it–and succinctly, while I was writing my “wall of text” here.  I’ll still share it since I do offer a couple more ideas and resources that may help.
I’ll still share it since I do offer a couple more ideas and resources that may help.
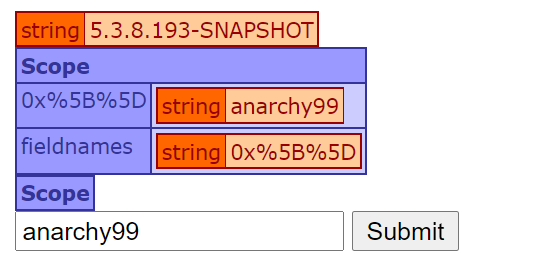
I assume, @purdue512, that you’re error handling is catching an error as thrown when cfqueryparam protects you from sql injection, which is great of course.
1] To your question of how to cause error handling to better manage the sending of a flood of such errors, some may want to say “don’t send an email on EACH error, but instead track them in a db and then send an email at intervals SUMMARIZING a group of errors”.
And there are in fact “error handling frameworks”, some written in cfml and some as services (both easy to use), which can imbue that sort of intelligence and more into your error handling. I keep a list of those as a category of my cf411 list, specifically:
https://www.cf411.com/error
2] But still another way to go would be to instead block those kind of hack attempts BEFORE they get to the queries, using any of various OTHER forms of protection, whether at the app, web server, or web app firewall levels. I keep also a list of each such types of protection tools (and a couple more) at:
https://www.cf411.com/protection
3] But finally, the simplest path may seem to be that you could detect in the error handling that the error is a failure specifically of a cfqueryparam, then you could perhaps ignore sending an email about THAT…but then you may miss “legit” failures cause by code mistakes or user input errors…
So then you may consider other options, like perhaps passing the input to any of the various cfml functions that “sanitize” a given string, and so skip sending the error to yourself if the sanitized result differs from the original (meaning it failed the sanitization check)…but that could be an unreliable approach for various reasons…
Or you could choose to skip sending the error if generated from the same ip in several seconds…but then sometimes bad guys do things to change their ip address to hide from such checks…
So then we’re back to, “leave it to the error handling framework makers to alert those things out”. That’s indeed part of why they exist, to “handle this” for us.  I don’t know if all of them handle those last 3 issues specifically (and I don’t suspect any handle the second), but a couple are open source CFML, so one could add such new intelligence to them, to help other users.
I don’t know if all of them handle those last 3 issues specifically (and I don’t suspect any handle the second), but a couple are open source CFML, so one could add such new intelligence to them, to help other users.
Let us know if any of these help.